
Cyber Security and Customer Experience
An Introduction for CX professionals (Part 3)
You have received a promotional email from a business vendor, but something seems . . . fishy.
You click on a legitimate-looking link that takes you to a fraudulent website. You close the window immediately and delete the email. Still, you’re worried the link may have somehow compromised your Privacy.
Unfortunately, cyber-attacks are becoming an increasingly common and unavoidable aspect to using Internet-reliant services for both consumers and businesses. A cyber-attack is an attack launched from one or more computers against another computer Watch this to see it in action.
Because of their multiple purposes and formats, CX teams should work in collaboration with IT Security and Privacy teams to help build secure customer journey’s by helping them understand the customer persona’s and their paths of engagement for receiving products and services.
In the third part of this series, we’ll examine common cyber-attacks, the CX touchpoints they can effect and an example of Persona’s and cyber characteristics.
Types of cyber attacks
Some of the most common types of cyber-attacks include:
- ● Malware
- ● Ransomware
- ● Malvertising
- ● Drive by download attacks
- ● Customer journey hacking
- ● Man-in-the-middle attacks
- ● Phishing
#1: Malware
You’ve probably experienced a malware attack at least once in the form of a virus, worm, or spyware, among other types. Though malware attacks typically don’t physically damage computers, malware can help hackers steal and delete information, hijack the computer, and observe users’ computer activities.
#2: Ransomware
Ransomware is a type of malware used to take control of a user’s device and/or encrypt their files. Users must pay a “ransom” to get their device and data back. Though Microsoft found that random ransomware attacks have decreased in the past few years, hackers are now shifting to creating ransomware that targets specific individuals, businesses, and sectors.
#3: Malvertising
Criminals use malvertising, or malicious advertisements, to trick website visitors into clicking an ad and downloading malware, visiting an unsafe website or server. Once the malware is installed from the malvertisement, hackers can take control of the computer, hold it for ransom, and/or steal personal information.
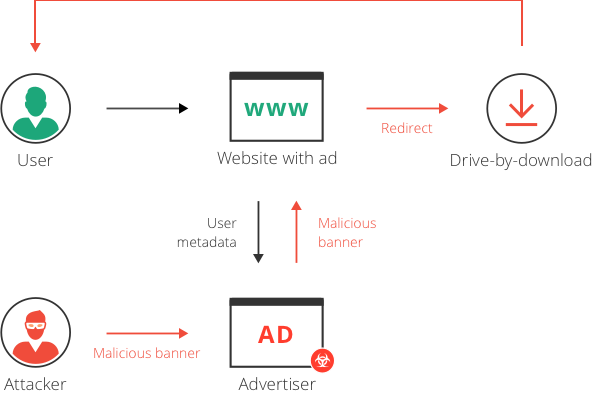
#4: Drive by download attacks
Drive by download attacks installs harmful programs without users’ approval. Drive by download attacks occur when hackers add damaging elements to websites. Users don’t even need to click anywhere on a page for a drive by download attack to occur – viewing the page is all that’s needed for the unwanted programs or files to install themselves.

#5: Customer journey hacking
Customer journey hacking involves using third-party code –often as an unauthorized advertisement — to divert customers to complete their purchase elsewhere. Besides being a nuisance to shoppers, research has found 78% of consumers would view an e-commerce website negatively as a result of seeing unauthorized ads.
#6: Man-in-the-middle (MiTM) attacks
During a man-in-the-middle attack, a bad actor will insert themselves in an interaction between two groups (such as a consumer and a business) to steal sensitive information. They come in multiple forms, such as wi-fi eavesdropping, IP spoofing, and email hijacking.
#7: Phishing
During a phishing attack, a hacker’s goal is to impersonate a legitimate organization using email, a phone call, or other type of communication so they can steal information. Phishing attacks are among the more common types of cyber-attack, with the Anti-Phishing Working Group (APWG) detecting over 199,000 phishing attacks in the third quarter of 2020 alone.
Section #2: Touchpoints vulnerable to cyber attacks
Nearly every touchpoint in a customer’s journey is susceptible to cyber-attacks. While not exhaustive, some particularly vulnerable touchpoints include:
#1: Business websites and products
Determined hackers can find holes on even the most secure sites. For example, a cybercriminal group compromised over 300 million browsing sessions to direct U.S. iOS users to websites promoting adult content and gift card schemes. Similarly, nearly 3,000 Australians have been targeted by malware affecting outdated versions of the Internet Explorer browser that attempts to steal device information, passwords, and files.
Businesses can stand to gain $5.2 trillion USD by defending against direct and indirect cyber-attacks. Closing holes in your business’ website is an excellent way to increase security while decreasing future costs.
#2: Business communication
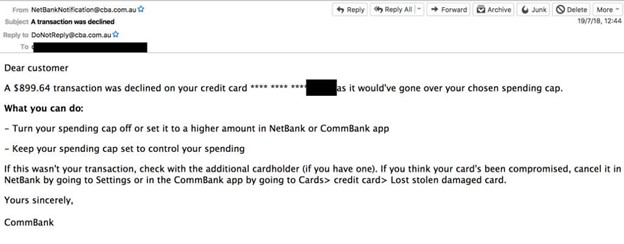
65% of cyber criminals use spear phishing emails, or emails targeting specific individuals, as their primary attack tool.
This may be partly because criminals can access scores of data with just one stolen email or phone number. Canada’s MacEwan University lost $11.8 million in an online phishing scam (illustrated below) where a malicious actor posed as one of the university’s vendors.

Similarly, Western Australian Premier, Mark McGowan, was sent an email containing an advanced type of malware from the Indonesian Embassy in Canberra. Hackers allegedly accessed a diplomat’s inbox, completed an email draft, and hid the malware in an attachment.
While the WA government intercepted the email, the malware could have caused significant damage.
As these examples show, it’s critical for business to give as much attention to employee cyber education as to their cyber infrastructure – part 4 in this series will go into this in more detail.
#3: Purchasing
Financial information is among the most immediately valuable data for criminals and makes the checkout process a prime target. For example, malware was found on Puma’s Australian website. The malware logged customers’ credit card numbers, names, and addresses, and then sent them to a server in Ukraine. Newegg, an electronics retailer experienced a cyber attack in late 2018 that affected customers’ checkout experience. Using just 15 lines of code, hackers installed malware on Newegg’s server that directed customers to a phony Newegg site when checking out.
While criminals can hack checkout processes with ease, making just a few security changes could save many of your customers from attack.
#4: Business-related touchpoints
Businesses may experience disruptions to their workflow, lose customer and employee trust, and face lawsuits if they don’t secure critical internal touchpoints. Three touchpoints worth securing immediately include:
Internal infrastructure and employee education

Weak security infrastructure and cyber-naive employees can increase the chances of being a cyber-attack victim. Over 250 million Microsoft customers saw their customer service and support data because of an error made in their database. In fact, 34% of data breaches were attributed to human error between January and June of 2020 in Australia alone.
Besides poor internal processes, employee ignorance can welcome cyber-attacks, too.
First American, a real estate insurance company, saw nearly 900 million records affected because of a technical error. Though they were warned about the vulnerability, they did not act on it. Though not all breaches may be on this same scale as Microsoft or First American, businesses should treat all threats and attacks with the same level of seriousness.
By focusing both on technological security and employee awareness, CX and IT teams can start building more cyber secure experiences.
Internal business operations
Cyber-attacks can interrupt organizations’ internal operations, and subsequently, their customers’ experiences. Lion Beer Australia experienced a ransomware attack that led them to temporarily shut down their system. The shutdown disrupted their vendors, customers who were trying to reopen their businesses after COVID-19 restrictions, and their supply chain.
Because of cyber attacks’ domino-like effects, brands should create backup plans for key businesses processes, so they’ll face minimal disruptions.
Old domains
Domain jacking occurs when a bad actor registers a domain without the original owner’s approval. This can be especially damaging for businesses with old domains from past promotions and products. 83% of the Forbes Global 2000 businesses are estimated to be at a greater risk for domain jacking because of poor domain security.

Domain jacking can yield a significant amount of data with surprisingly little effort. For example, this cyber security researcher domain jacked several law firms’ old domains. He was able to receive emails containing debit card numbers (as in the screenshot below), legal documents, valid passwords, and access to other online accounts, among other sensitive information.
For the sake of both your business’ and customers’ security, make sure to keep a list of domain names and retire them properly when your business no longer needs them.
Create secure customer journeys that stay one step ahead of cyber criminals
Creating secure customer experiences requires collaboration between multiple departments and perhaps even partnerships with external experts and governmental bodies.
Regardless of your taskforce’s size, there are some key steps in creating a secure customer journey.
Firstly, familiarize all employees of the types of cyber threats that could compromise customers’ security. Secondly, examine your Customer Personas their paths of engagement for receiving products and services. This understanding is expressed as well-defined consumer personas, each with its own assigned characteristics, behavior, attitudes, and pain points. Refer example persona below.

Areas of the customer journey that have the most security holes or are the most desirable to hackers, and gradually work to secure them from the most to the least vulnerable.
Admittedly, it can take months or even years to sufficiently design end-to-end secure customer journeys. However, taking steps towards building secured customer experiences today can pay off is a great way to build momentum for farther-ranging future projects.
In the final article of this four-part series, I’ll share my tips on how to build a business-wide cyber secure culture in even small- to medium-sized businesses. If you’re just reading part 3 here’s a link to part 1 and part 2 of the series.
In the interim, I would recommend you enrol in the upcoming Customer Experience Excellence Course in February 2021 to enhance your knowledge of the six customer experience competencies and prepare for the Certified Customer Experience Professional (CCXP) exam.
Resources
- 250 Million Microsoft Customer Service Records Exposers; Exactly How Bad Was It?
- All about malware
- Are You Vulnerable to Domain Hijacking?
- Attackers Load Targeted Company’s Homepage in Email Phishing Campaign
- The Cost of Cybercrime: Ninth Annual Cost of Cybercrime Study
- COVID-19 Related Malvertising Targets Outdated Versions of Internet Explorer
- D’oh! Beer Company Suffers Cyber Attack
- Domain Security Report — Forbes Global 2000 Companies
- Drive-By Downloads and How to Prevent Them
- Hacking law firms with abandoned domain names
- Internet Security Threat Report: Volume 24 | February 2019
- MacEwan University defrauded of $11.8M in online phishing scam
- Malvertising
- Malvertising
- Man in the middle (MITM) attack
- Microsoft Security Endpoint Threat Summary 2019
- Newegg Hacked to Steal Customers’ Credit Card Data
- Notifiable Data Breaches Report: January-June 2020
- Online Consumer Behavior Survey: Optimizing the Journey for Today’s Multi-Tasking Shopper
- Phishing Activity Trends Report: Unifying the Global Response To Cybercrime
- Puma Australia shoppers hit with credit card hack, researchers say
- Questions raised over alleged Chinese hacking attempt on WA Premier Mark McGowan’s office
- Ransomware
- Security Oversight at First American Causes Data Leak of 900 Million Records
- The Silent E-Commerce Sales Killer: Customer Journey Hijacking
- US iOS users targeted by massive malvertising campaign
- What is a Drive by Download: Everything You Need to Know
- What is Malvertising?
- What Is Malware?
- What is a man-in-the-middle attack?
- What is Phishing?
- What is spear phishing? Why targeted email attacks are so difficult to stop
- Building Security into the Customer Experience – McKinsey & Company












Recent Comments